Smart Business IoT: How CSPs are Using RAD’s Solution to Enhance Asset Management
Sep 14, 2024

The Internet of Things (IoT) is transforming how businesses operate, and Communication Service Providers (CSPs) are key to this change, as they can provide the connectivity and infrastructure necessary for a robust IoT ecosystem.
The digital transformation is affecting businesses of all sizes, in almost every industry. This presents a significant market opportunity for CSPs to move up the value chain and enhance their offering beyond basic connectivity.
Recognizing this shift, RAD is providing CSPs with its Smart Business IoT solution, allowing business customers to access asset management services to help them in their digital journey.
Key Takeaways:
- RAD’s Smart Business IoT integrates smart sensors, IoT gateways, and a centralized platform, providing business users with real-time data collection, analysis, and visualization – as well as reports and alerts – for efficient asset management.
- Businesses can monitor their in-building assets for critical conditions like temperature, humidity, and movement in real-time, ensuring operational efficiency, regulatory compliance, and cost savings.
- As an optional out-of-the-box solution, customers can easily set it up, without requiring IT technical resources they normally don’t have.
- Smart Business IoT can be applied in various industries, such as retail and food services, to monitor equipment performance. Such businesses can benefit from improved business insights, data-driven decision-making, and enhanced customer service.
What is Smart Business IoT Solution?
Smart Business IoT provides communication service providers with everything their business customers need to monitor their assets remotely. The package integrates smart sensors, an IoT gateway, and a centralized IoT platform dashboard, which provides real-time and historical asset reporting. For example, a grocer can monitor critical conditions such as temperature, humidity, and movement in real-time. This ensures operational efficiency and compliance with regulatory standards.
The Evolution of IoT: A Growing Opportunity for CSPs
According to a survey we commissioned among 220 CSPs around the world, and which is available in the report “Top Trends in CSP IoT and Private 5G Campus Services”, CSPs recognize the growing demand for IoT and are ready to capitalize on this opportunity. Service providers are beginning to develop and launch specific offerings for enterprises who are utilizing IoT as part of their core business, beyond the provision of simple data plans that enable network connectivity.
IoT Services Provided, 2022-2024. Source: RAD
They are targeting many different verticals, including Healthcare, Retail, Manufacturing, Public Utilities, and Smart Cities. However, the most prominent sectors for IoT services are healthcare (55%), industry and manufacturing (50%), and retail (43%). In fact, 95% of service providers include IoT as part of their offering.
Digital transformation is set to make a real difference for businesses, who typically rely on manual operation of routine tasks. By integrating digital tools, enterprises can drive significant efficiencies that impact staff, customers, and ultimately, the bottom line. A large part of this transformation process is applied to asset management.
By offering remote asset management services, CSPs can assist their customers become more efficient as well as increase customer satisfaction and comply with regulations.
What is Asset Management and Why is it Important for Businesses?
Asset management allows remote and automated monitoring of in-building assets, to ensure their proper operation. For example, a grocer can use it to find out that their refrigerator is not working before it causes a loss of inventory. Asset monitoring identifies inefficiencies and optimizes operations before they become costly.
Let’s dig a bit deeper into our example. In addition to the cost of goods, a grocery store must also comply with health and safety regulations. If the business isn’t digitized, then this means that, twice a day, an employee must check and log the temperature for all cold and hot-holding units to ensure that perishable items are being stored at safe temperatures. A fully digitized process clearly saves the cost of manpower needed, with the added benefit of periodic reports, alerts and insights. With a proper IoT-based asset management service, business owners and operations managers can get data remotely and make informed decisions, such as when it’s time to restock, or schedule maintenance.
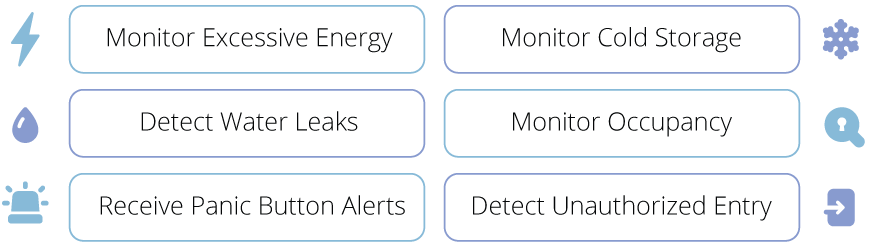
Here are a few examples of types of remote asset monitoring for businesses:
RAD’s Smart Business IoT
RAD’s Smart Business IoT solution is easy to implement and does not require special technical expertise. It includes pre-configured sensors, a gateway and an intuitive dashboard:
Smart Sensors: Monitor critical conditions like temperature, humidity, and movement.
IoT Gateway: Ensure seamless data transmission from sensors to the cloud-based IoT platform.
IoT Platform: Central hub for data collection, analysis, and visualization.
Users receive periodic reports from collected data points to keep tabs on their business. In addition, they receive alerts when operations are disturbed so that they can act immediately, as well as receive AI-based insights that can help them run their business better. In turn, they can reduce their costs, increase their own customers’ experience, comply with regulations, and meet their ESG (environmental, social, and governance) goals.
Alternatively, if the business has some elements already in place, the solution can be easily integrated into them.
As we’ve explored throughout this article, asset management has become a necessity in today’s competitive business landscape. RAD’s Smart Business IoT solution offers benefits for both CSP and their business customers. Traditionally known for providing connectivity services, CSPs are now evolving their business models to offer more comprehensive IoT solutions that can scale with business growth. They can move up the value chain and become true partners in their customers’ digital transformation journeys.
To learn more about RAD’s Smart Business IoT solution, read this solution brief.